CASTIEL DEFENSE
WE DON’T JUST DEFEND THE INNOCENT
WE HUNT THE ENEMY

NEED ASSISTANCE FOR AN ACTIVE
CYBER CRIME?
CALL: +1 720-703-8207

Exclusive Services
-
Identity Ghosting
Identity Ghosting is our specialized service designed to systematically erase or minimize your digital and physical identity footprint, helping you reclaim privacy in an increasingly connected world. Through expert techniques like data removal from public databases, online profile scrubbing, and secure identity management strategies, we reduce your visibility to trackers, advertisers, and potential threats.
This service is ideal for high-profile individuals, professionals in sensitive industries, victims of harassment or identity theft, or anyone seeking to protect their personal information from unwanted exposure.

-
Cyber Private Investigations
Cyber Private Investigations is our expert service focused on uncovering digital truths through ethical and legal online research, data analysis, and forensic techniques. We delve into cyber trails to gather evidence on matters like online fraud, cyberstalking, intellectual property theft, or background verifications, using advanced tools to trace digital footprints while adhering to privacy laws.
This service benefits individuals suspecting online deception, businesses protecting assets from digital threats, legal professionals needing cyber evidence, or anyone requiring discreet online inquiries to resolve personal or professional concerns.

-
Adversarial Cyber TacticAL Defense Training & Workshop
Adversarial Cyber Tactical Defense Training & Workshop is our immersive program that equips participants with essential knowledge to combat evolving digital threats. Through engaging presentations, we explore modern attacks employed by cybercriminals, inherent security vulnerabilities in AI systems and surveillance technologies, and proven strategies to safeguard against them.
Optional hands-on workshops offer practical simulations in a controlled environment, allowing attendees to experience and counter techniques like hacking, social engineering, and breaching scenarios to build real-world defensive skills.


CASTIEL DEFENSE SOLUTIONS


S
// SERAPHIM LOGIC
A
A
ZERO POINT IMPACT SINCE 2020
ai email & Sandbox Detonation analysis
With over 24 computer-vision and text analysis models see an email much like a person does - only betterA
As phishing techniques evolve with alarming sophistication, detecting attacks that bypass conventional filtration systems has become exceedingly challenging—if not impossible—for end users. At Castiel Defense, we've remained one step ahead. Since 2020, zero clients have experienced phishing-related impacts with Seraphim Logic, a testament to the unparalleled effectiveness of our Zero Point architecture, seamlessly integrated with Seraphim Logic’s cutting-edge analysis system.
Over 15 BILLION Compromised Assets Identified
70+ AV / Intelligence Engines Integrated
80+ Domain Scanning Engines

// HAWKEYE WIRELESS
WE Identify and hunt wireless threats
ARE YOU BEING FOLLOWED?
IS SOMEONE TRYING TO WIRELESSLY ATTACK YOU?
ARE ACTIVE DRONES IN YOUR NEAR PROXIMITY?


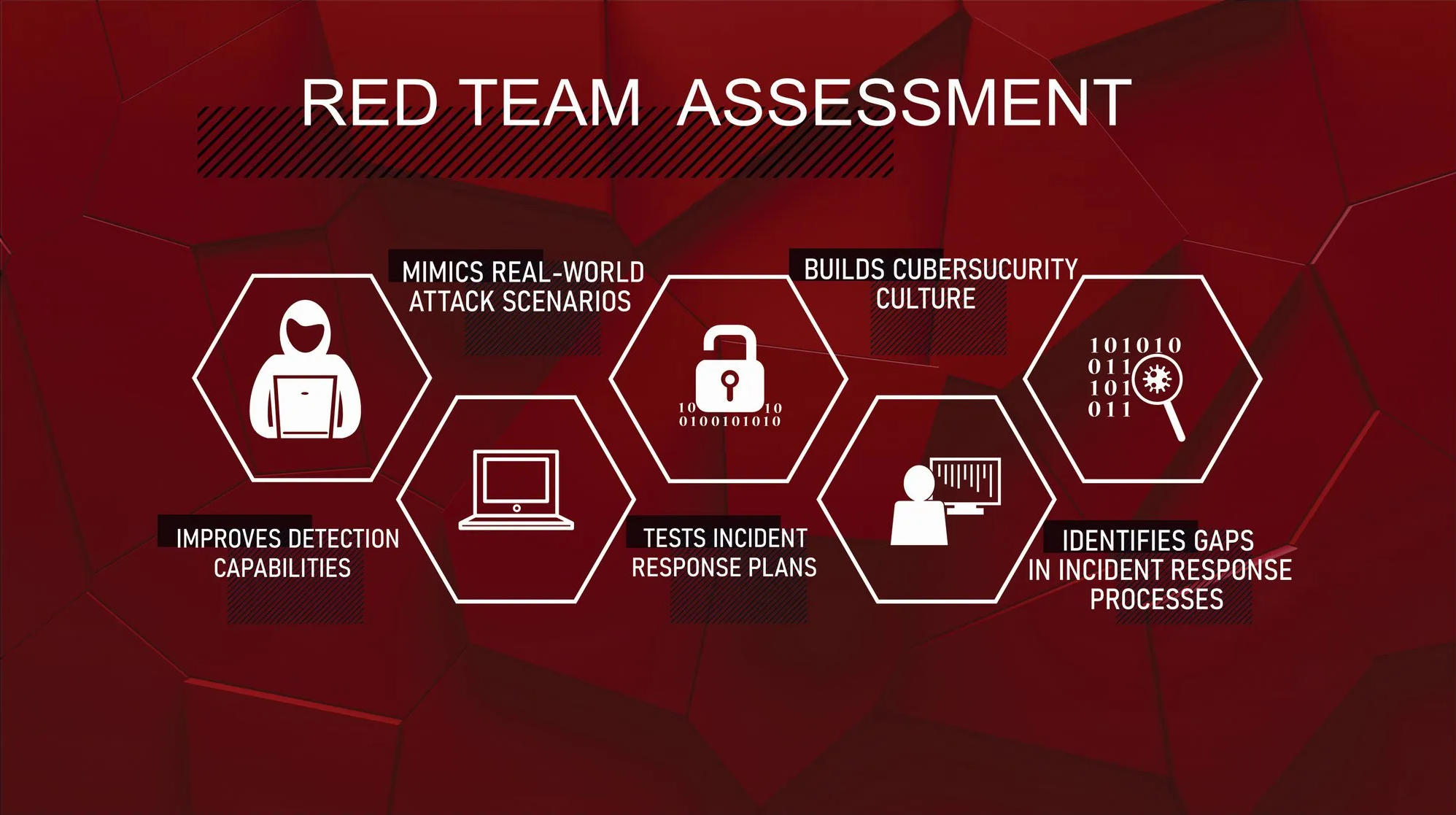
// PenTesting & Red Teaming
Penetration Testing (Pentesting) and Red Teaming are proactive cybersecurity services designed to identify vulnerable security gaps and strengthen your defensive capabilities in your business’s digital and physical defenses.
Pentesting involves simulated cyberattacks to uncover weaknesses in systems, networks, or applications, providing actionable insights to fortify your infrastructure.
Red Teaming takes it further, mimicking real-world adversaries with advanced tactics like social engineering, physical breaches, and custom exploits to test your organization’s overall security posture. These services help ensure compliance with industry standards, and enhancing resilience against cyber threats. By identifying gaps before attackers do, Pentesting and Red Teaming protect sensitive data, safeguard customer trust, and prevent costly breaches, empowering your business to stay one step ahead in today’s threat landscape.


“OUR EFFORTS HAVE INTERCEPTED MILLIONS IN ILLICIT FUNDS, RESCUED KIDNAPPED CHILDREN, AND AVERTED TERRORIST ATROCITIES THAT COULD HAVE CLAIMED COUNTLESS LIVES.”
- HUNTING WITH A PURPOSE